A new zero-day vulnerability has been discovered in Google Chrome, sending shockwaves through the cybersecurity world. CERT-In, India’s cybersecurity agency, has issued a high-severity warning. The vulnerabilities impact specific versions of Google Chrome on Windows and Mac running versions before 124.0.6367.201/.202 and on Linux versions before 124.0.6367.201. This critical flaw could allow attackers to exploit your system before a patch is available, making it a race against time to protect your data. Google is urging users to update their browsers immediately to the latest version to protect their devices from potential exploits.
But what exactly is a zero-day vulnerability, and why should you be concerned? In essence, it’s a software flaw that is unknown to the vendor, giving hackers a window of opportunity to exploit it before a fix is released. This leaves users vulnerable, with no immediate defense against potential attacks. In this article, we’ll delve into the intricacies of zero-day vulnerabilities, explore the potential risks they pose, and provide actionable steps you can take to safeguard your digital life. From understanding the mechanics of these exploits to learning how to mitigate their impact, we’ll equip you with the knowledge you need to stay one step ahead of cyber threats.
Demystifying Zero-Day Vulnerabilities
Imagine a secret passageway into your home that you didn’t know existed. That’s essentially what a zero-day vulnerability is to software – an unknown and unguarded entrance that malicious actors can exploit to wreak havoc. But how are these vulnerabilities discovered in the first place? Let’s lift the veil and peek into the world of zero-day discovery.
Unearthing these hidden vulnerabilities is a complex dance between various players:
- Security Researchers: These digital detectives meticulously analyze software code, searching for weaknesses that could be exploited.
- Ethical Hackers: These “white hat” hackers work with companies to find and report vulnerabilities before the bad guys can exploit them.
- Malicious Actors: Unfortunately, not everyone has good intentions. Some hackers actively seek out zero-days to use for their own nefarious purposes.
- Bug Bounty Programs: Many tech companies offer rewards to researchers who find and report vulnerabilities, incentivizing them to help keep software safe.
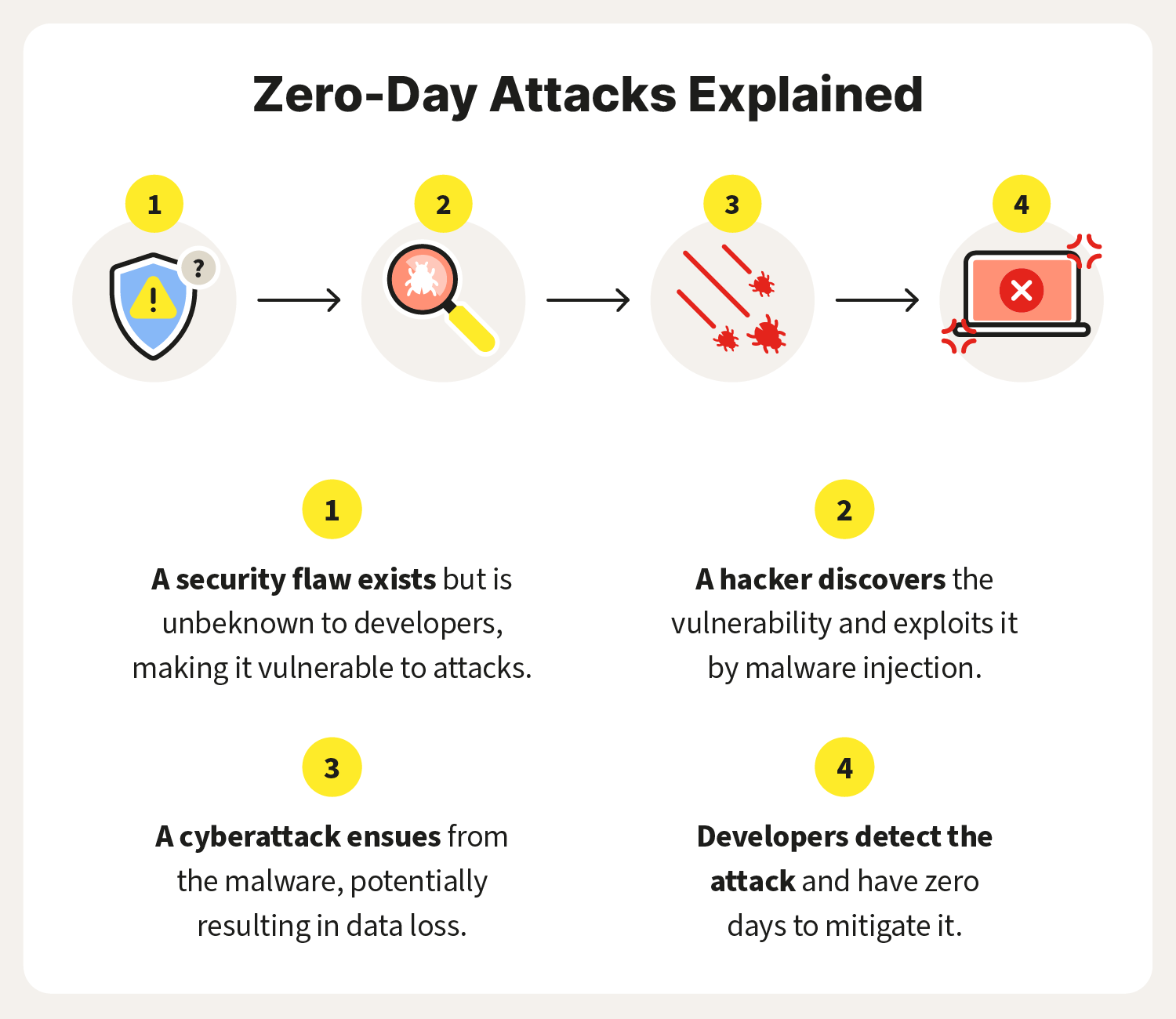
The Zero-Day Lifecycle: A Race Against Time
The journey of a zero-day vulnerability follows a predictable yet urgent path:
- Discovery: A researcher or hacker stumbles upon the vulnerability.
- Disclosure: The finder decides whether to report it to the vendor (responsible disclosure) or keep it secret (irresponsible disclosure).
- Patching: The vendor scrambles to develop a fix and release a patch to users.
- Exploitation: If the vulnerability is known before it’s patched, attackers can exploit it to cause damage.
Source: Norton
Types of Zero-Day Vulnerabilities: A Sneak Peek
Zero-day vulnerabilities come in various forms, each with its unique way of wreaking havoc:
- Buffer Overflows: These occur when a program tries to store more data than it can handle, potentially allowing attackers to execute their own code.
- Injection Attacks: Hackers inject malicious code into a program, tricking it into executing harmful commands.
- Privilege Escalation: This allows attackers to gain higher-level access to a system than they should have, opening the door to further mischief.
Understanding how zero-day vulnerabilities are discovered and the different forms they can take is crucial for comprehending the broader landscape of cybersecurity threats. By knowing what we’re up against, we can better prepare ourselves to defend against these hidden dangers lurking in the digital world.
When Zero-Days Strike: A Pandora’s Box of Cyber Chaos
Zero-day vulnerabilities aren’t just theoretical threats lurking in the shadows of the digital realm. They’re real-world weapons that have unleashed havoc on individuals, businesses, and even entire nations. Let’s take a closer look at some high-profile examples that underscore the devastating impact of these exploits.
Real-World Zero-Day Attacks: A History of Havoc
- Stuxnet (2010): This sophisticated worm, believed to have been developed by the U.S. and Israel, targeted Iran’s nuclear program. It infiltrated industrial control systems and caused physical damage to centrifuges used for uranium enrichment, effectively setting back Iran’s nuclear ambitions.
- WannaCry (2017): This ransomware attack infected hundreds of thousands of computers worldwide, encrypting files and demanding payment in Bitcoin for their release. Hospitals, businesses, and government agencies were crippled, causing massive financial losses and disrupting essential services.
- SolarWinds Hack (2020): This sophisticated supply chain attack compromised the software of SolarWinds, a major IT management company. The attackers gained access to the networks of numerous government agencies and Fortune 500 companies, potentially stealing sensitive data and compromising national security.
The Ripple Effects: A Tsunami of Consequences
The impact of zero-day attacks extends far beyond the immediate victims. They can trigger a cascade of devastating consequences for individuals and organizations alike:
- Individuals:
- Financial loss: Identity theft, stolen credit card information, fraudulent charges.
- Reputational damage: Leaked personal data, embarrassing photos or videos, compromised online accounts.
- Emotional distress: Anxiety, fear, loss of privacy, sense of violation.
- Organizations:
- Financial loss: Ransomware payments, data recovery costs, regulatory fines, lost revenue.
- Reputational damage: Loss of customer trust, negative media coverage, shareholder lawsuits.
- Operational disruption: System downtime, lost productivity, service interruptions.
- Legal liability: Potential lawsuits from customers, employees, or partners.
Targeted Attacks: The Precision Weapons of Cyberwarfare
Zero-day vulnerabilities are particularly prized by nation-states and cybercriminals for targeted attacks. These exploits allow them to bypass traditional security measures and gain access to highly sensitive systems and information.
Nation-states use zero-days for espionage, sabotage, and even acts of war. Cybercriminals use them to steal valuable data, extort money, or disrupt critical infrastructure. In both cases, the consequences can be severe and far-reaching.
The threat of zero-day attacks might seem daunting, but don’t despair! There are practical steps you can take to fortify your digital defenses and minimize your risk of falling victim to these sneaky exploits.
1. Update, Update, Update:
Think of software updates like a suit of armor that gets stronger with each patch. When developers release updates, they’re often fixing vulnerabilities, including zero-days, that could leave your system exposed. Make it a habit to install updates promptly, not just for your operating system, but for all your applications and browsers too.
2. Practice Good Cyber Hygiene:
It’s not just about washing your hands; good cyber hygiene is essential for keeping your digital self healthy. This means:
- Strong Passwords: Create unique, complex passwords for each account, and consider using a password manager to keep track of them.
- Two-Factor Authentication (2FA): Add an extra layer of security by requiring a code from your phone or another device to log in.
- Cautious Clicking: Don’t click on suspicious links or open attachments from unknown senders.
- Secure Browsing: Use a secure browser and avoid risky websites.
- Regular Backups: Back up your important data regularly to an external hard drive or cloud storage.
3. Build a Multi-Layered Defense:
Think of cybersecurity like a castle with multiple layers of protection. To keep out the invaders, you’ll need more than just a strong password. Consider these additional defenses:
- Firewall: This acts like a gatekeeper, controlling incoming and outgoing network traffic.
- Antivirus and Anti-Malware Software: These tools scan your system for malicious code and can help prevent infections.
- Intrusion Detection Systems (IDS): These monitor your network for suspicious activity and can alert you to potential threats.
4. Stay Vigilant and Monitor for Suspicious Activity:
Even with the best defenses, it’s important to remain vigilant. Keep an eye out for any unusual activity on your accounts or devices. This could include:
- Unexpected password reset emails
- Unauthorized login attempts
- Unusual charges on your credit card
- Unexpected emails or messages from friends or family
The Bottom Line
Zero-day vulnerabilities are a serious threat to our digital world. They can be used to cause significant harm to individuals and organizations. It’s crucial to understand the risks and take steps to protect yourself and your organization from these attacks. If you notice anything suspicious, take action immediately. Change your passwords, contact your bank or credit card company, and report any suspicious activity to the appropriate authorities. Remember, cybersecurity is an ongoing process. Stay informed about the latest threats, keep your software updated, and practice safe online habits. By taking these steps, you can significantly reduce your risk of falling victim to a zero-day attack and keep your digital life secure.
____________
Written By: TEchquity india